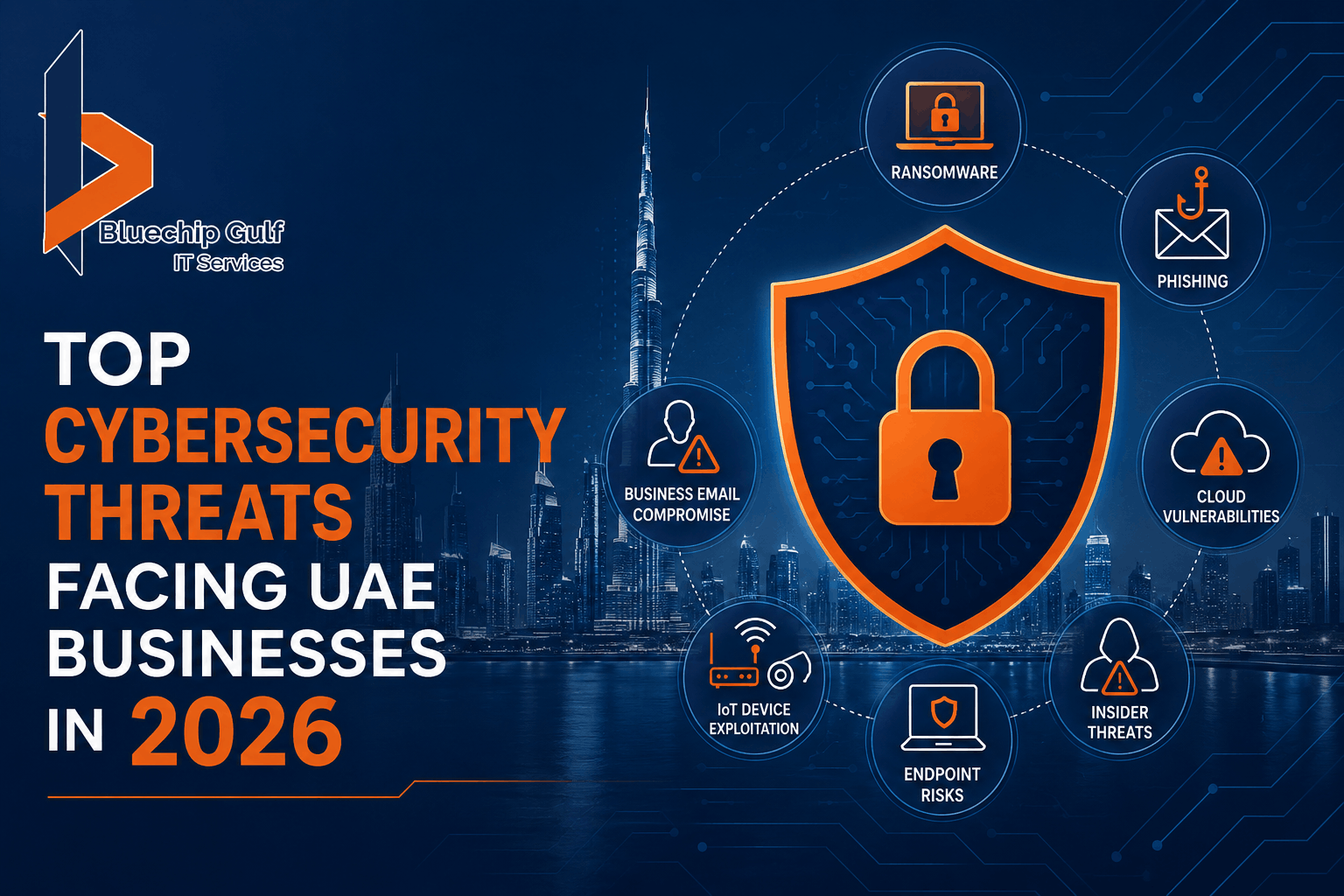
As UAE businesses continue adopting cloud technologies, AI tools, and remote work environments, cybersecurity threats are becoming more advanced in 2026. From ransomware and phishing attacks to cloud security risks and data breaches, organizations across the UAE face growing challenges in protecting their digital infrastructure.
 This article highlights the top cybersecurity threats businesses should watch for and how to stay protected against evolving cyber risks.
This article highlights the top cybersecurity threats businesses should watch for and how to stay protected against evolving cyber risks.
1. AI-Powered Phishing Attacks
Phishing attacks are becoming harder to detect because attackers now use AI-generated emails, fake voice calls, and impersonation tactics that closely mimic real communication.
Employees may unknowingly:
- Share login credentials
- Open malicious attachments
- Transfer sensitive information
- Install malware unknowingly
Modern Anti-Virus and Anti-SPAM Solutions help filter suspicious emails and reduce phishing risks before they reach employees.
2. Ransomware Attacks
Ransomware remains one of the most dangerous threats for UAE companies in 2026.
Attackers encrypt company data and demand payment to restore access.
Businesses often experience:
- Operational downtime
- Financial losses
- Reputation damage
- Data recovery costs
Organizations without proper backup strategies and security monitoring are especially vulnerable.
3. Cloud Security Vulnerabilities
As more UAE companies move toward cloud-based infrastructure, cloud misconfigurations are becoming a major security concern.
Common issues include:
- Weak access permissions
- Exposed storage systems
- Poor identity management
- Insecure APIs
Without proper monitoring, sensitive business data may become publicly accessible.
4. Insider Threats
Not all cybersecurity threats come from external attackers.
Disgruntled employees, accidental data leaks, or poor internal security practices can expose sensitive information.
This is why businesses are strengthening access control policies and implementing advanced monitoring systems.
5. Business Email Compromise (BEC)
Cybercriminals frequently target executives and finance departments through fake invoices or impersonation emails.
These attacks often appear highly legitimate and can result in:
- Fraudulent payments
- Financial theft
- Vendor impersonation
- Data exposure
Email security and employee awareness training play a major role in reducing these attacks.
6. IoT and Smart Device Exploitation
Smart offices, surveillance systems, IoT devices, and connected infrastructure create additional entry points for attackers.
Poorly secured devices can allow unauthorized access to internal networks.
This is becoming increasingly important as UAE businesses continue adopting smart office technologies and automation systems.
7. Weak Endpoint Security
Remote work has expanded the number of laptops, smartphones, and personal devices connected to business networks.
Without centralized endpoint protection, attackers can compromise devices through:
- Malware
- Unsafe Wi-Fi networks
- Unpatched systems
- Unauthorized software
Businesses are increasingly deploying enterprise-grade Data Protection Systems to secure endpoints and sensitive company data.
 How UAE Businesses Can Reduce Cybersecurity Risks
How UAE Businesses Can Reduce Cybersecurity Risks
Implement Advanced Firewall Protection
Modern Firewall Systems help monitor and filter network traffic to block malicious activities before they enter the organization.
Next-generation firewalls provide:
- Intrusion prevention
- Application monitoring
- Threat intelligence
- Real-time traffic analysis
Strengthen Endpoint Protection
Businesses should deploy:
- Enterprise anti-virus software
- Endpoint detection systems
- Device monitoring solutions
- Automated patch management
This helps reduce risks across remote and onsite devices.
Backup and Disaster Recovery Planning
Regular backups ensure businesses can recover quickly after ransomware or data loss incidents.
Cloud backup and disaster recovery strategies are becoming essential for operational continuity.
Employee Security Awareness Training
Human error remains one of the biggest cybersecurity weaknesses.
Regular training helps employees identify:
- Phishing emails
- Suspicious links
- Social engineering attacks
- Unsafe downloads
Continuous Security Monitoring
24/7 monitoring helps businesses detect unusual activities before they become serious security incidents.
Managed security services are increasingly popular among UAE organizations that lack dedicated internal security teams.
Industries Most Targeted in the UAE
Cyber attackers frequently target:
- Financial institutions
- Government entities
- Healthcare providers
- Logistics companies
- Retail businesses
- Real estate firms
- Oil & gas companies
These industries handle valuable customer and operational data.
Final Thoughts
Cybersecurity threats in the UAE are becoming more advanced, automated, and financially damaging every year. Businesses that rely only on basic protection methods may struggle to defend against modern attack techniques in 2026.
Organizations investing in advanced Firewall Systems, proactive monitoring, employee awareness, and enterprise-grade protection strategies will be far better prepared to manage evolving cyber risks.
Reliable cybersecurity solutions partners like Bluechip Gulf help UAE businesses strengthen their digital infrastructure through comprehensive protection, monitoring, and managed security solutions.
Businesses looking to improve cybersecurity resilience can explore services offered by Bluechip Gulf for advanced threat protection and enterprise security support.

 How UAE Businesses Can Reduce Cybersecurity Risks
How UAE Businesses Can Reduce Cybersecurity Risks