
Privileged Access Management (PAM) is a specialized cybersecurity solution within identity management that secures, controls, manages, and monitors elevated (“privileged”) access to critical assets.In 2026, Abu Dhabi’s technical landscape will be more than only a regional powerhouse; it will be an international beacon for smart city innovation and sovereign digital transformation.
As companies in the capital increase their journey into cloud-native architectures and AI-driven functions, the keys to the kingdom, privileged accounts, have become the eventual prize for cyber adversaries.
Whether you’re a government unit, a financial powerhouse in the ADGM, or an expanding company in the industrial domain, the change from conventional protection to a forceful identity-first model is no longer optional. This is why privileged access management in Abu Dhabi has emerged as the cornerstone of contemporary cybersecurity methods.
Understanding the Keys to the Kingdom – What are PAM and PIM?

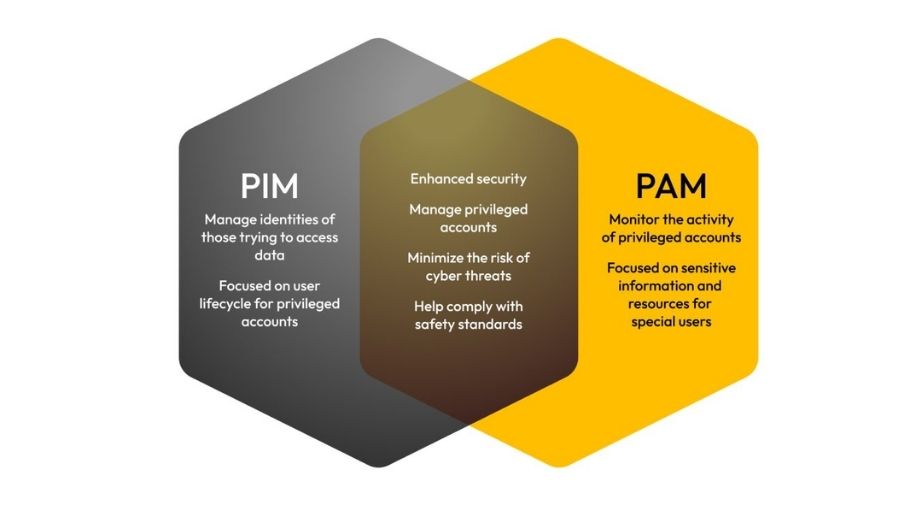
Before moving ahead, it is crucial to streamline the terminology. While usually grouped together, PAM and PIM serve two different but complementary duties in your protection share.
- Privileged Access Management
PAM concentrates on the tools and strategies utilized to protect, control, and supervise access to crucial systems. Consider PAM as the guard at the door of your data center or server. It makes sure that even if somebody has a key, their actions are recorded, their sessions are timed, and their approvals are restricted to precisely what they have to do.
- Privileged Identity Management
PIM is more about the lifecycle and governance of the recognitions themselves. It answers the question – who is permitted to have a key in the first place? PIM manages the activation of duties, making sure that a user only becomes an Admin for a particular window of time instead of having permanent, standing privileges that can be abused.
Together, PAM/PIM solutions in Abu Dhabi deliver a dual-layered protection that handles both the identity and the access.
Why Abu Dhabi Enterprises Must Prioritize PAM & PIM in 2026

The capital’s remarkable economic position and stringent regulatory environment make it a high-stakes environment for information protection. Here are the main drivers for adopting these solutions today.
- Compliance with NESA and ADGM Regulations
Abu Dhabi has some of the world’s strongest data security and information assurance norms.
- National Electronic Security Authority – The UAE Information Assurance Standards mandate strict controls more than T5.2.2 – Restrict and control the distribution and use of privileges.
- ADGM Data Protection Regulations – For financial entities, showing Data Protection by Design is impossible without granular control over who can access sensitive financial statements.
Failing to execute these controls can cause remarkable penalties, but more crucially, it puts your license to run in crucial industries at risk.
- Combating the Rise of AI-Driven Identity Theft
By 2026, cybercriminals will utilize Attack-as-a-Service tools and generative AI to craft ideal phishing campaigns. Once a single credential is stolen, attackers look for lateral movement, the capability to jump from a common user account to a privileged admin account.
A strong PAM solution prevents this movement cold by demanding multi-factor authentication and biometric verification for every privileged action.
- Securing a Hybrid and Remote Workforce
The contemporary Abu Dhabi company is not confined to a single office in Al Maryah Island. With employees, vendors, and consultants accessing systems from across the world, the network perimeter has vanished. PAM/PIM solutions in Abu Dhabi permit you to give protection and temporary access to third-party vendors without providing them permanent passwords to your internal network.
The Strategic Role of Information Security Consultancy

Executing PAM and PIM isn’t a plug-and-play task. It demands a profound knowledge of your business workflows to make sure that protection does not become a bottleneck for efficiency. This is where expert information security consultancy becomes invaluable. A consultant assists your company –
- Discover Hidden Risk – Recognizing shadow admin accounts that were made years ago and forgotten.
- Define the Least Privilege Model – Making sure employees have only sufficient access to do their jobs, and nothing more.
- Automate Compliance – Establishing systems that automatically produce the audit logs needed by UAE regulators.
Collaborating with the Best – Bluechip Abu Dhabi

When it comes to protecting the capital’s technical future, Bluechip Abu Dhabi stands at the forefront of digital superiority. As a premier provider of managed IT and protection services, Bluechip delivers a top-notch system for privileged access management in Abu Dhabi.
Their specialization spans from initial vulnerability evaluations to the full-scale deployment of zero-trust architectures. By collaborating with Bluechip, companies achieve access to –
- Local Expertise – A group that comprehends the particular regulatory landscape of the United Arab Emirates.
- 24/7 Monitoring – Making sure that any unusual privileged activity is flagged and neutralized in seconds.
- End-to-End Governance – Handling the whole recognizing lifecycle, from onboarding new executives to offboarding departing contractors.
Key Features to Demand in a 2026 PAM/PIM Solution
If you are presently considering vendors, confirm your solution includes these four “must-have” features –
Feature | Why It Matters |
| Just-In-Time (JIT) Access | Permissions are only granted when a task is started and revoked immediately after. |
| Session Recording | Every action an admin takes is recorded in a video-like format for total accountability. |
| Credential Vaulting | Passwords are encrypted and hidden; even the admin doesn’t “know” the password they are using. |
| Behavioral Analytics | AI monitors if an admin’s behavior changes (e.g., accessing a database at 3 AM from an unusual IP). |
Conclusion
Identity is the new perimeter in 2026. Protecting your privileged accounts is now a business necessity that safeguards your data, your reputation, and your bottom line. It is no longer merely an IT task.
You can make sure your business is resilient to changing threats by incorporating cutting-edge PAM / PIM solutions in Abu Dhabi and collaborating with a reliable information security consultancy.
